
Pattern Locks Are Unsafe Secure Your Xiaomi Redmi K70 Phone Now with These Tips

Pattern Locks Are Unsafe: Secure Your Xiaomi Redmi K70 Phone Now with These Tips
Pattern locks have been available for about as long as people can remember, and they have been hugely popular with people thanks to how easy it is to simply swipe your screen and unlock your smartphone, as against, say, keying in the 4-digit PIN/ 6-digit PIN. However, pattern locks are easy to crack, and today, we bring you all you want to know about pattern locks and how to create a hard pattern lock. Further to this, we also tell you how to move beyond pattern locks and what to do in case you forgot the hard pattern lock you just set and are unable to unlock your smartphone.
Part 1: What You Need to Know About Pattern Locks
Pattern lock is an Android-only feature that makes it easy for users to have a modicum of security on their smartphones. Most users do not prefer using and remembering a PIN to unlock the smartphone. Creating a pattern makes it easier, somehow.
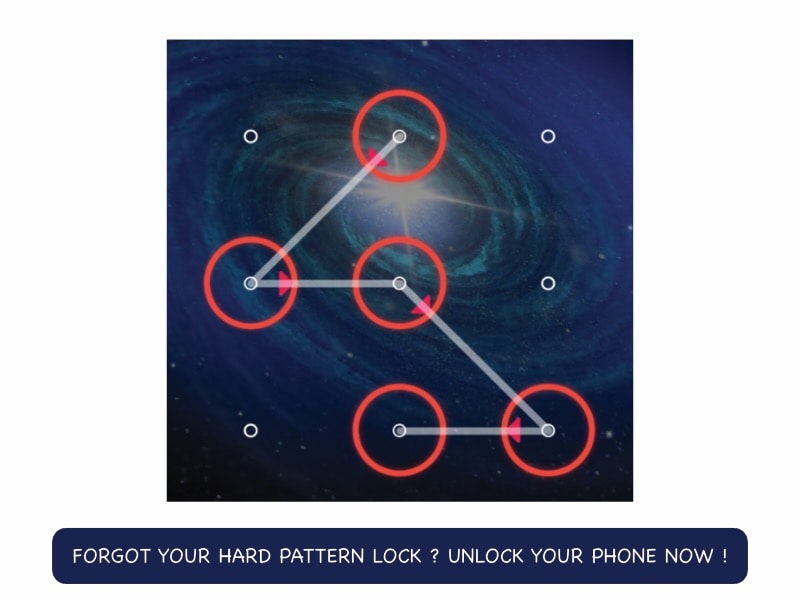
There is a 9-point grid on which you swipe your finger from point to point, in any direction, and when you take your finger off, that pattern you swiped becomes the key to unlock your smartphone.
Pattern locks were exceedingly common only a few years ago, and they are not recommended for use any longer due to concerns (mentioned later in the article).
1.1: Popularity and Usage
Old habits die hard, or so they say, right? That’s because it is true. We are creatures of habit, and pattern locks have been around for a long, long time. We are accustomed to pattern locks. So, even with even easier technologies such as fingerprint recognition and face recognition, we tend to gravitate towards the familiar old pattern lock.
The only thing is, there is a reason why pattern locks are no longer the preferred option to use for unlocking your smartphones. As it happens, that reason is security, and it can be very easy for humans to take a swipe (pardon the pun) at your pattern lock. And guess what? The research conducted suggests that they would get it right with an unsettling accuracy.
1.2: Advantages and Drawbacks
With on-the-go lifestyles, our smartphones have become indispensable and contain some of the most sensitive aspects of our lives – IDs, credit and debit cards in digital wallets, photo and video memories, business documents – you name it, the smartphones have it, on the go. This has opened our lives up to the public at large, and if someone steals our smartphone or, best case, finds it, the only barrier preventing them from being privy to all that wealth of our sensitive information is that screen lock – the pattern lock that we set on our smartphones. That’s it – the single pattern lock stands between malicious actors and our data. You might be beginning to realize just how crazy this is.
Advantages of Pattern Locks
There are two advantages to using pattern locks. One, they are better than nothing. Two, they are easy to use. And that’s about it. There is no third advantage to pattern locks. We might think we set a hard pattern lock that nobody could guess, but, as research proves, we might be thinking too low of human prowess.
Disadvantages of Pattern Locks
Security, or rather, the lack of it, is the lone disadvantage of using a pattern lock. What good is a pattern lock that can be easily deciphered? Sure, they are easy to use, and they are better than not having anything, but would you really want to protect your life’s data with something that could be, as researchers found out, breached in under 5 attempts? We don’t think you do!
The research found that 64% of test subjects who were shown videos of people unlocking their phones could correctly guess a 6-point pattern lock, that too after viewing the video only once! That number shot up to 80% if they were allowed to see the video again. That is simply astounding and a nightmare for security. When it comes to PINs, only 11% could guess a 6-digit PIN after viewing the unlocking video once, and that number shot up to 27% when they could see the video two times.
Part 2: How To Create a Hard Pattern Lock (Including Remembering Complex Patterns)
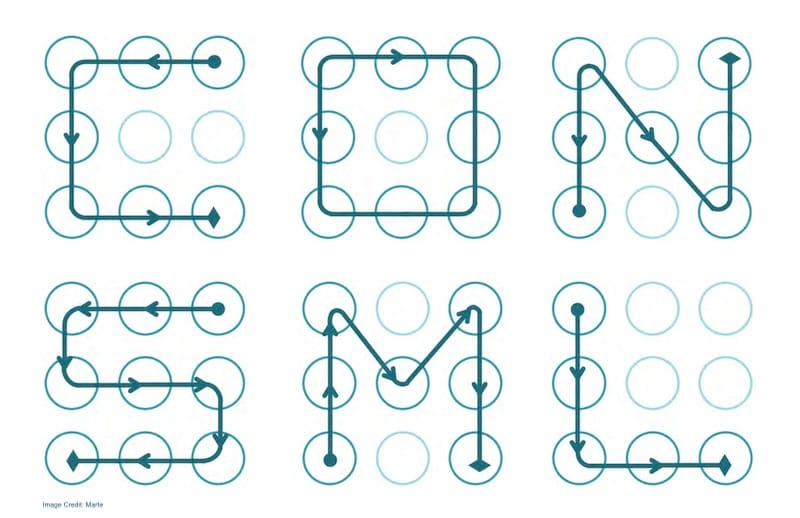
Now, if you must continue using a pattern lock, let’s help you know how to create a hard pattern lock that would not be as easy to decipher as easy pattern locks. For that, you should know how people use pattern locks, the kind of pattern locks they create, and the ones that are the most commonly used pattern locks. That way, you can avoid those fallacies and create a hard pattern lock for your smartphone.
2.1: The Pattern Locks People Use Most Commonly
Marte Loge, an M.Sc. Computer Science student, gave a presentation on pattern locks at DEFCON 23 and made a bold claim. She said, “Tell me who you are, and I will tell you your lock pattern.”
She presented the following statistics to support her claim:
- - In her research, she found that 77% of people started with one of the 4 corners when creating a pattern lock.
- - 44% of people started with the top-left dot and 15% with the top-right, while the bottom-left was preferred by 14% of her test subjects.
- - People set 5-point pattern locks on average, and most users were content with a 4-point pattern.
These are some of the most common pattern locks people create:
- - patterns in the shapes of alphabets,
- - patterns in the shapes of numerals,
- - patterns in any other simple shape, such as square, triangle, star, etc.
To understand how this is a security nightmare, the possible combinations for a 4-point pattern are a measly 1624, whereas by adding just 1 more point to the pattern and creating a 5-point pattern, the number of possible combinations becomes 7152, an increase of 5528 combinations. In stark contrast, creating a 9-point pattern would give you over 140,000 possible combinations!
2.2: How to Create a Hard Pattern Lock
Knowing what most people do when creating a pattern lock, it becomes easy to avoid those mistakes and instead create a hard pattern lock for oneself.
- - Do not start creating a pattern lock from any of the 4 corners of the grid.
- - Never use your first initial as your pattern lock.
- - Never use the shape of a numeral as your pattern lock.
- - Use all 9 points on the grid to create your pattern lock, and contrary to popular belief, you can go over the connecting lines several times, creating a hard pattern lock that would not be as easy for people to decipher!
Part 3: Going Beyond Pattern Locks
You might think that now that you have set a hard pattern lock, you are good to go. Hardly. Technology has evolved, so have methods to break into your device.
Step 1: Set a 6-digit PIN
The minimum you should do today is set a 6-digit PIN to unlock your phone. Consider this a necessary investment into the safety of your data residing on your smartphone.
Step 2: Use Fingerprint Recognition (or Face Recognition on Apple Devices)
All modern smartphones released over the last decade have come with fingerprint recognition. Using fingerprint recognition requires you to set a 6-digit PIN and then set a fingerprint to unlock your device. You can set additional fingerprints, too.
This way, your device is the most secure it can be today. In case your fingerprint is not recognized for any reason, the phone falls back on the 6-digit PIN that you can enter and unlock your phone.
While face recognition is available on both Android and Apple devices, it is truly secure only on Apple devices. This is why Apple iPhones released after the iPhone X in 2017 have come only with Face ID. They fall back on a minimum 6-digit PIN (called Passcode in Apple world) to unlock in case the face does not get recognized in the first attempt.
Part 4: How To Unlock Phone If Hard Pattern Lock Forgotten
Just in case you set a hard pattern lock and promptly forgot that abstruse pattern you just set, we have a tool for you to quickly unlock your phone in case of a forgotten hard pattern lock: Wondershare Dr.Fone - Screen Unlock.

Dr.Fone - Screen Unlock (Android)
Remove the Hard Pattern Lock on Your Xiaomi Redmi K70 If You Forgot!
- Remove all Android screen locks (PIN/pattern/fingerprints/face ID) in minutes.
- Bypass the FRP lock of Samsung without a PIN or Google account.
- Everyone can handle the lock screen without any tech knowledge.
- Provide specific removal solutions to promise good success rate.
4,008,671 people have downloaded it
Download the latest version of Dr.Fone from the Wondershare website and launch the app.
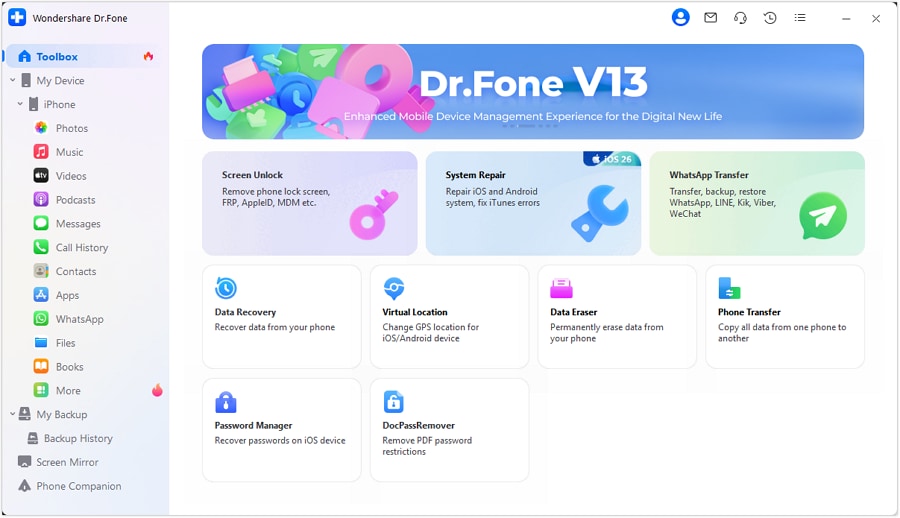
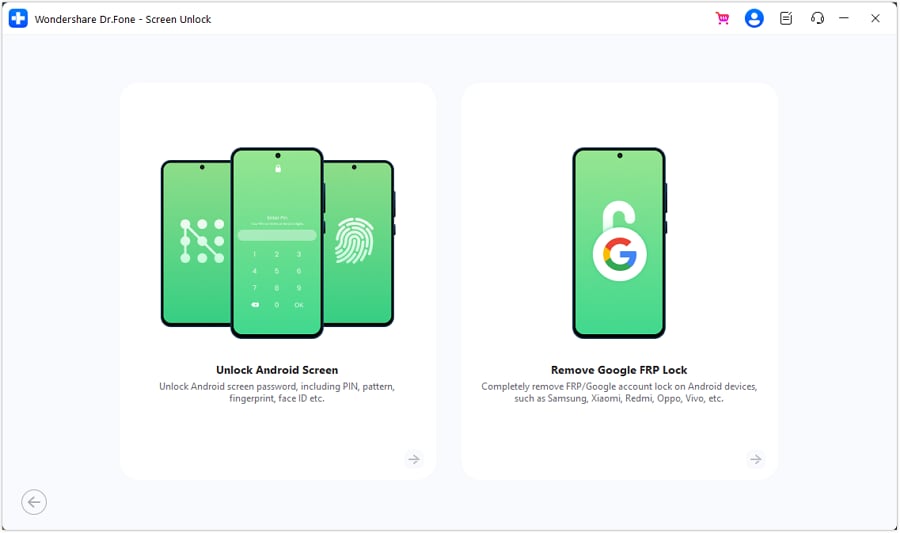
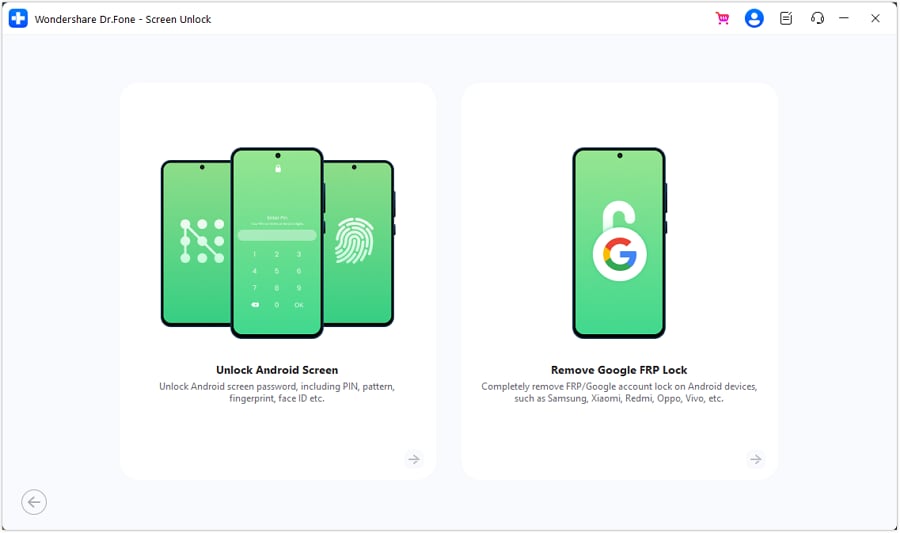
Step 1: Click Android under Toolbox > Screen Unlock.
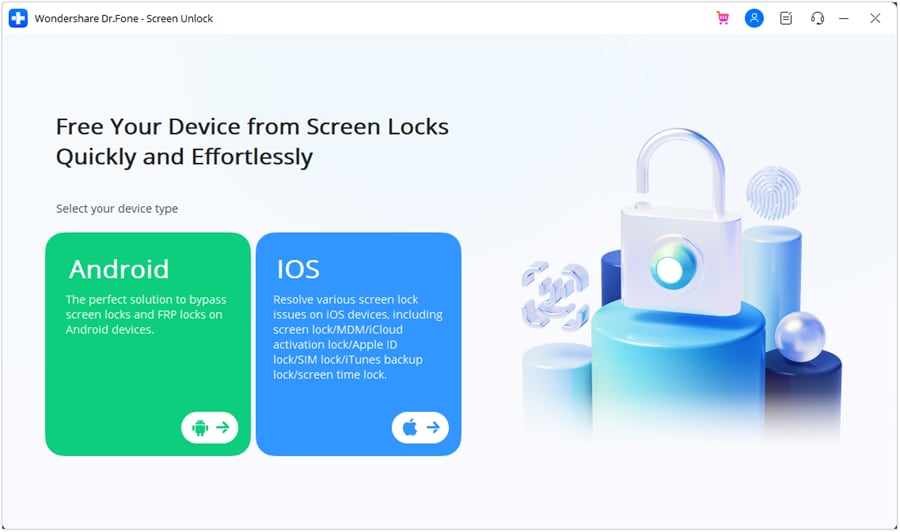
Step 2: Click Unlock Android Screen.
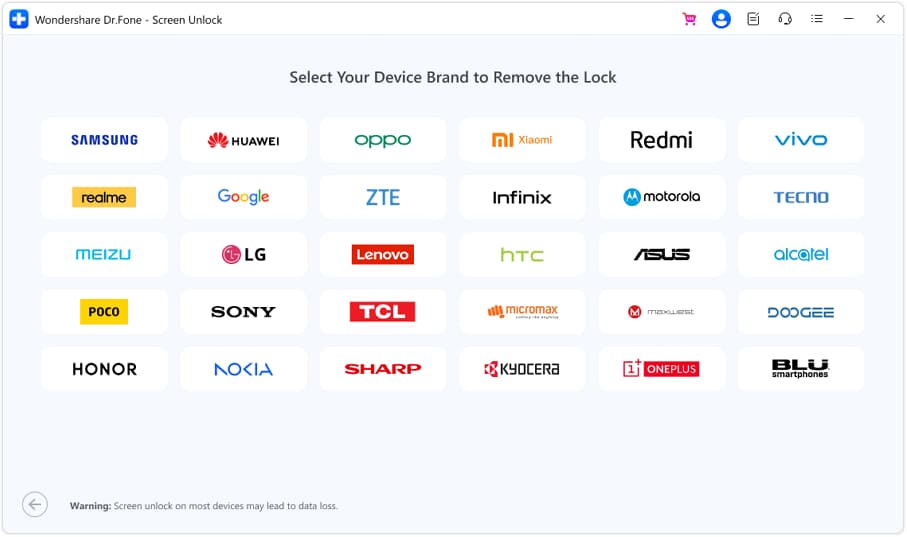
Step 3: Select your device manufacturer.
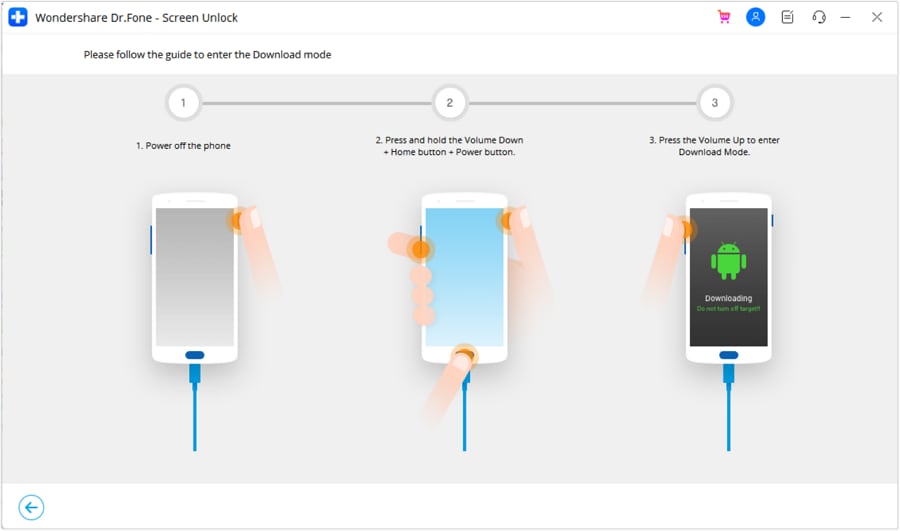
Step 4: Prepare your device to unlock the screen.
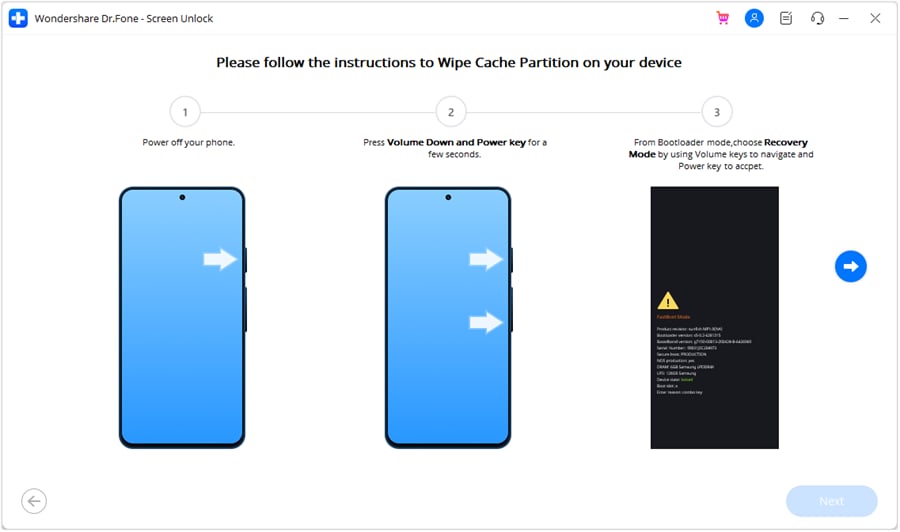
When the greyed Next button becomes available, click it and wait for your device to be unlocked.
All data on the Xiaomi Redmi K70 device is wiped under this method. Select Samsung phones may be unlocked without data loss. Check this list for devices that may be unlocked without data loss.
Closing Words
Whether it is an easy pattern lock or a hard pattern lock, the fact is that pattern locks are antiquated and a security nightmare. A minimum 6-digit PIN must be used, and using fingerprint recognition is the preferred way to go for Android devices. Using fingerprint recognition will require that users create a 6-digit PIN. On Apple devices launched after 2017, there is Face ID, Apple’s marketing term for face recognition. If you did indeed still set a hard pattern lock, only to promptly forget it, use Wondershare Dr.Fone – Screen Unlock (Android) to seamlessly unlock your phone right now.
Top 10 Password Cracking Tools For Xiaomi Redmi K70
What is password cracking?
Password cracking process involves recovering a password from storage locations or from data, transmitted by a computer system on network. Password cracking term refers to group of techniques used to get password from a data system.
Purpose and reason of password cracking includes gaining an unauthorized access to a computer system or it can be recovery of forgotten password. There might be another reason of using password cracking technique that is for testing password strength so hacker could not hack into system.
Password cracking is normally performed thought repetitive process in which computer applies different combinations of password till the exact match.
Brute Force Password Cracking:
Term brute force password cracking may also be referred as brute force attack. Brute force password cracking is respective process of guessing password, in this process software or tool creates a large number of password combinations. Basically it’s a trail-and-error technique used by software to obtain password information from system.
A brute force attack are normally used by hackers when there is no chance of taking advantage of encrypted system weakness or by security analysis experts to test an organization’s network security .This method of password cracking is very fast for short length passwords but for long length passwords dictionary attack technique is normally used.
Time taken by brute force password cracking software to crack password is normally depend upon speed of system and internet connection.
GPU Password Cracking:
GPU is graphics processing unit, sometimes also called visual processing unit. Before talking about GPU password cracking we must have some understanding about hashes . When user enter password the password information stored in form of computer hashes using the one-way hashing algorithm.
In this password cracking technique using GPU software take a password guess and look through hashing algorithm and compare it or match it with the existing hashes till the exact match.
GPU can perform mathematical functions in parallel as GPU have hundreds of core that gives massive advantage in cracking password. GPU is much faster than CPU so that’s the reason of using GPU instead of CPU.
CUDA Password Cracking:
CUDA Compute Unified Device Architecture is a model for programming and a platform that perform computations in parallel, created by NVIDIA for graphic processing.
CUDA Password cracking includes cracking passwords using Graphics card which have GPU chip, GPU can perform mathematical functions in parallel so the speed of cracking password is faster than CPU.GPU have many 32bit chips on it that perform this operation very quickly.
We can easily access CUDA through libraries, directives and with the help of different programming languages that includes C, C++ and FORTRAN.
Password Cracking Tools
Given below is the list of Top10 Password cracking tools.
1. Cain and Abel : Top password cracking tool for Windows
Cain & Abel is one of the top cracking tool for password cracking and password recovery for Windows OS.
Cain & Abel can use techniques of Dictionary Attack, Brute-Force and Cryptanalysis attacks to crack encrypted passwords. So it only uses the weakness of system to crack password. GUI Interface of software is very simple and easy to use. But have availability limitation, tool only available for window based systems .Cain & Abel tool have many good features some of the features of tool are discussed below:
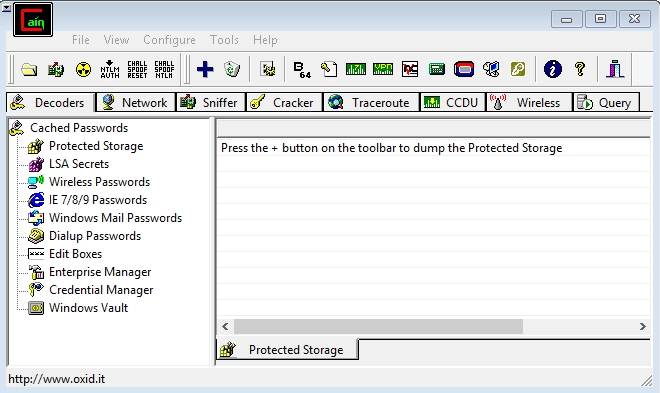
Features of Cain & Abel:
- Used for WEP (Wired Equivalent Privacy) cracking
- Have ability to record conversation over IP
- Cab be used as Network Password Sniffer
- Ability to resolve addresses IP to MAC.
- Can crack verity of hashes including LM and NT hashes, IOS and PIX hashes, RADIUS hashes, RDP passwords, and lots more than that.
Site for Download:
2. John the Ripper : Multi-platform, Powerful, Flexible password cracking tool
John the Ripper is a free multi or cross platform password cracking software. Its called multi platform as it combines different password cracking features into one package.
It’s primarily used to crack weak UNIX passwords but also available for Linux, Mac, and Windows. We can run this software against different password encryptions including many password hashes normally found in different UNIX versions. These hashes are DES, LM hash of Windows NT/2000/XP/2003, MD5, and AFS.
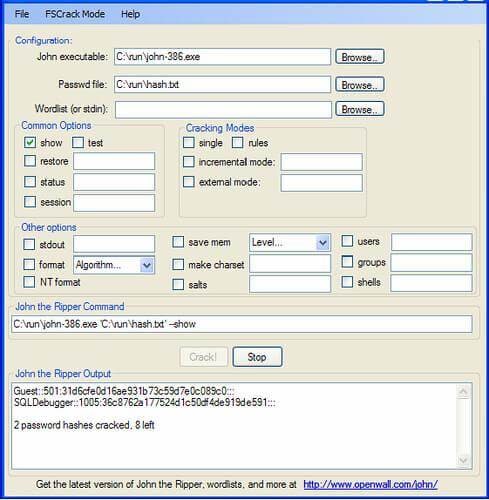
Features of John the Ripper
- Supportive with Brute force password cracking and dictionary attacks
- Multi platform
- Available free for use
- Pro version is also available with additional features
Site for Download:
3. Aircrack : Fast and effective WEP/WPA cracking tool
Aircrack is a combination different tools used for Wifi, WEP and WPA passwords cracking. With the help of these tools you can crack WEP/WPA passwords easily and effectively
Brute force, FMS attack, and dictionary attacks techniques can be used to crack WEP/WPA passwords. Basically it collects and analyzes encrypted packets then using its different tool crack password out of the packets. Although aircrack is available for Windows but there are different issues with this software if we use this in Windows environment, so it’s best when we use it in Linux environment.
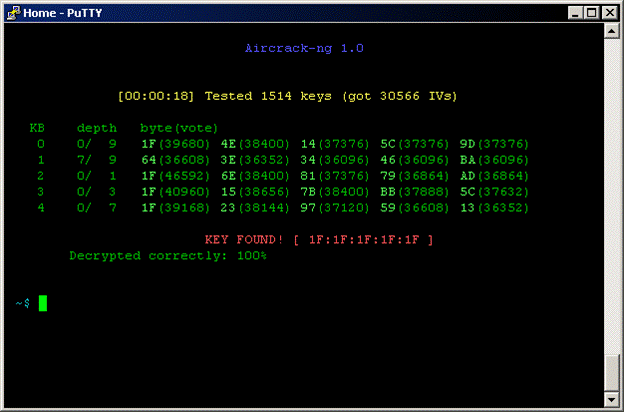
Features of Aircrack
- Supportive with both Brute force and dictionary attacks cracking techniques
- Available for Windows and Linux
- Available in live CD
Site for Download:
4. THC Hydra : Multiple services supportive, Network authentication cracker
THC Hydra is a supper fast network password cracking tool. It uses network to crack remote systems passwords.
It can be used to crack passwords of different protocols including HTTPS, HTTP, FTP, SMTP, Cisco, CVS, SQL, SMTP etc. It will give you option that you may supply a dictionary file that contains list of possible passwords. It’s best when we use it in Linux environment.

Features of THC Hydra
- Fast cracking speed
- Available for Windows, Linux ,Solaris and OS X
- New modules can be added easily to enhance features
- Supportive with Brute force and dictionary attacks
Site for Download:
https://www.thc.org/thc-hydra/
5. RainbowCrack : New Innovation in Password Hash Cracker
RainbowCrack software uses rainbow tables to crack hashes, in other words we can say it uses process of a large-scale time-memory trade for effective and fast password cracking.
Large-scale-time-memory-trade-off is a process of computing all hashes and plain text using a selected hash algorithm. After calculations, obtained results are stored in the tables called rainbow table. Process of creating rainbow tables is very time consuming but when its done software works very fast.
Password cracking using rainbow table is faster than the normal brute force attack method. It’s available for Linux and Windows operating system.
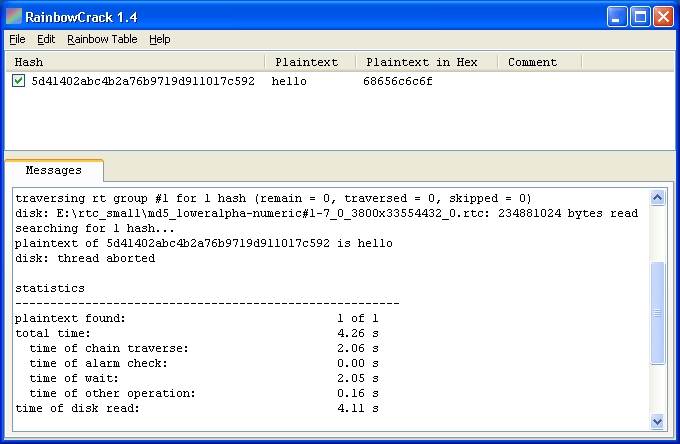
Features of Rainbow Crack
- Support verity of Rainbow tables
- Runs on Windows (XP/Vista/7/8) and Linux operating systems (x86 and x86_64)
- Simple in use
Site for Download:
http://project-rainbowcrack.com/
6. OphCrack : Tool for Windows password cracking
OphCrack used to crack Windows user passwords with the help of rainbow tables that are available in a bootable CD.
Ophcrack is completely free to download, Windows based password cracker that uses rainbow tables to crack Windows user passwords. It normally cracks LM and NTLM hashes. Software has simple GUI and can runs on different platforms.
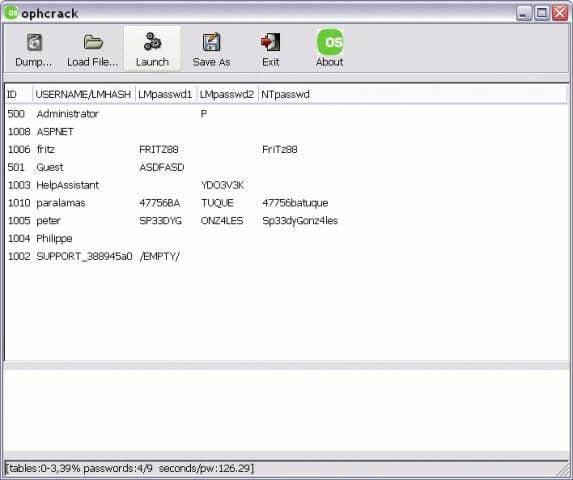
Features of OphCrack
- Available for Windows but also available for Linux, Mac, Unix, and OS X
- Uses for LM hashes of Windows and NTLM hashes of Windows vista.
- Rainbow tables available free and easily for Windows
- To simplify the process of cracking Live CD is available
Site for Download:
http://ophcrack.sourceforge.net/
7. Brutus : A brute force attack cracker for remote systems
Brutus is the fastest, most flexible, and most popular software used to crack remote system passwords. It guess password through applying different permutations or by using a dictionary.
It can be used for different network protocols including HTTP, FTP, IMAP, NNTP and other types such as SMB, Telnet etc. It also gives you facility of creating your own authentication type. It also includes extra options of load and resume, so process can be paused when required and you can resume process when you want.
It is only available for windows operation systems. Tool has a limitation that it has not been updated since 2000.

Features of Brutus
- Available for Windows
- Can be used with different network protocols
- Tool have many good extra features
- Support SOCK proxy for all types of authentications
- Capability of error handling and recovery
- Authentication engine is multi stage
Site for Download:
8. L0phtCrack : Smart tool for Windows password recovery
Just like OphCrack tool L0phtCrack is also a Windows passwords recovery tool uses hashes to crack passwords, with extra features of Brute force and dictionary attacks .
It normally gains access to these hashes from directories, network servers, or domain controllers. It is capable of doing hash extraction from 32 & 64 bit Windows systems, multiprocessor algorithms, scheduling, and can also perform decoding and monitoring networks. Yet it is still the easiest to use password auditing and recovery software available.
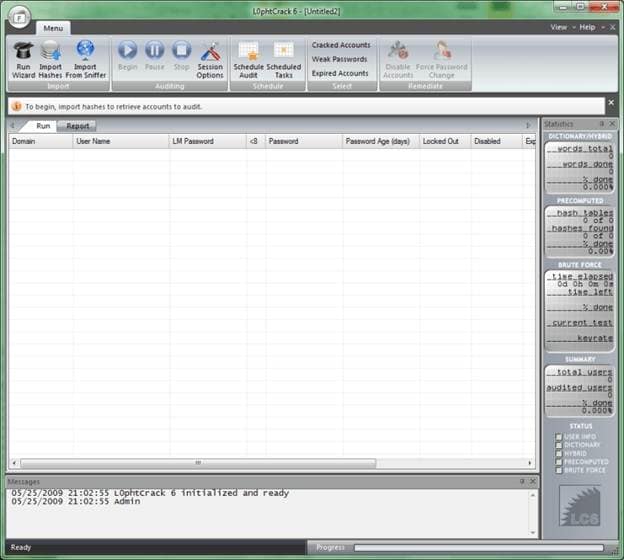
Features of L0phtCrack
- Available for Windows XP, NT, 2000, Server 2003,and Server 2008
- Can work in both 32- and 64-bit environments
- Extra feature of schedule routine auditing on daily, weekly, monthly bases
- After run it provide complete Audit Summary in report page
Site for Download:
9. Pwdump : Password recovery tool for Windows
Pwdump is actually different Windows programs that are used to provide LM and NTML hashes of system user accounts.
Pwdump password cracker is capable of extracting LM, NTLM and LanMan hashes from the target in Windows, in case if Syskey is disabled, software has the ability to extract in this condition.
Software is update with extra feature of password histories display if history is available. Extracted data will be available in form that is compatible with L0phtcrack.
Recently software is updated to new version called Fgdump as Pwdump not work fine when any antivirus program is running.
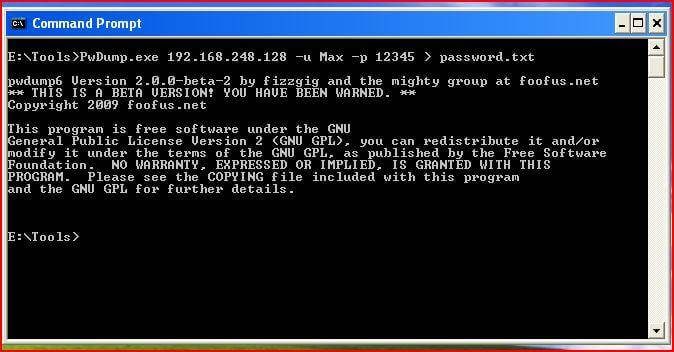
Features of Pwdump
- Available for Windows XP, 2000
- Powerful extra feature are available in new version of Pwdump
- Ability to run multithreaded
- It can perform cachedump (Crashed credentials dump) and pstgdump (Protected storage dump)
Site for Download:
10. Medusa : Speedy network password cracking tool
Medusa is remote systems password cracking tool just like THC Hydra but its stability, and fast login ability prefer him over THC Hydra.
It is speedy brute force, parallel and modular tool. Software can perform Brute force attack against multiple users, hosts, and passwords. It supports many protocols including AFP, HTTP, CVS, IMAP, FTP, SSH, SQL, POP3, Telnet and VNC etc.
Medusa is pthread-based tool, this feature prevent unnecessarily duplicate of information. All modules available as an independent .mod file, so no modification is required to extend the list that supports services for brute forcing attack.
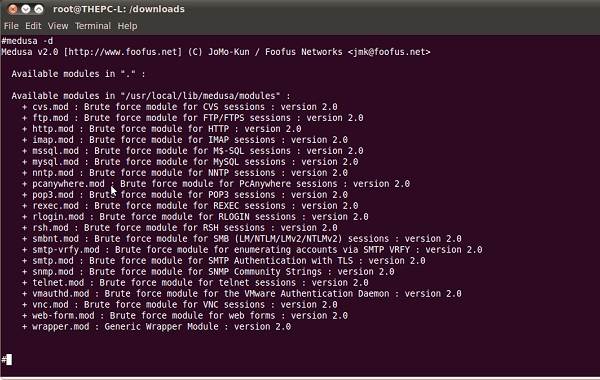
Features of Medusa
- Available for Windows, SunOS, BSD, and Mac OS X
- Capable of performing Thread based parallel testing
- Good feature of Flexible user input
- Due to parallel processing speed of cracking is very fast
Site for Download:
Top 12 Prominent Xiaomi Redmi K70 Fingerprint Not Working Solutions
Part 1. Optimal Solution: Unlock With Wondershare Dr.Fone Directly
Facing a malfunctioning fingerprint on your Xiaomi Redmi K70 can be frustrating. In this scenario, the most effective resolution is the removal of the registered fingerprint. Yet, traditional methods of removing the fingerprint can be difficult and pose security risks. In this case, going for tools like Wondershare Dr.Fone is the best choice. This tool ensures your Pixel device is at no risk.
Dr.Fone offers a swift solution to remove the Android lock screen in five minutes. It effectively removes 4 types of screen locks. These include patterns, PINs, passwords, and fingerprints. Dr.Fone can bypass the Android FRP lock without needing a PIN or Google account. It ensures accessibility to the Android device without such credentials.

Dr.Fone - Screen Unlock (Android)
The Best UnlockJunky Alternative to Bypass FRP and Solve Your Screen Locks
- Remove all Android screen locks (PIN/pattern/fingerprints/face ID) in minutes.
- Bypass the FRP lock of Samsung without a PIN or Google account.
- Everyone can handle the lock screen without any tech knowledge.
- Provide specific removal solutions to promise good success rate.
4,008,672 people have downloaded it
Prominent Features of Wondershare Dr.Fone
- FRP bypass is enabled for brands like Samsung, Xiaomi, Redmi, Oppo, Realme , and Vivo.
- With Dr.Fone, bypassing screen locks can be achieved without data loss.
- Fone supports 2000+ Android phones and tablets from over 18 brands for screen unlocking.
Step-by-Step Guide To Remove Fingerprint Type Lock on Google Pixel Using Dr.Fone
With Dr.Fone, you can resolve the Xiaomi Redmi K70 fingerprint sensor not working issue within minutes. Below is a detailed walkthrough for removing a fingerprint lock on a Google Pixel:
- Step 1: Connecting and Accessing Screen Unlock Feature on Dr.Fone
Open Wondershare Dr.Fone and connect your Android device via a USB cable. Once the connection is established, navigate to the “Toolbox” tab and choose “Screen Unlock.” Upon reaching the new screen, choose the “Android” option. Then, select “Unlock Android Screen” from the options on the following screen.
- Step 2: Selecting Google As the Xiaomi Redmi K70 device Brand and Activating Recovery Mode
Afterward, you’ll be guided to a subsequent screen prompting you to choose the Xiaomi Redmi K70 device brand, Google. Once you select the brand, you’ll be directed to enter a specific mode corresponding to it. For Google Pixel Devices, the specific mode to enter is Recovery Mode. Simply follow the on-screen instructions to activate Recovery Mode on your device.
- Step 3: Initiate the Fingerprint Removal Process
After entering Recovery Mode, the screen unlocking procedure will initiate automatically. Please wait for the fingerprint removal process to finish. In case of failure, select “Try Again” to attempt unlocking again. Upon successfully unlocking your Android device’s screen, tap “Done.”
Part 2. 11 Conventional Solutions To Resolve Pixel Fingerprint Not Working
The solution above using Wondershare Dr.Fone is an effective and comprehensive method. It can tackle fingerprint recognition issues, but sometimes, users may look for simpler alternatives. We will explore conventional solutions that can address Pixel fingerprint problems. Each solution will also explain the underlying reasons for the Pixel 6 fingerprint sensor issue.
1. Fingerprint Sensor Not Touched Firmly
Problem
If the fingerprint sensor fails to recognize your fingerprint, it might be due to inadequate pressure. This could also be due to improper finger placement on the sensor.
Solution: Firm Placement
Ensure you firmly place your finger on the sensor, covering it entirely. Avoid too much pressure, but make sure the sensor fully contacts your fingerprint.
![]()
Problem
Glitches or software bugs in your Pixel device may cause disruptions. This can include issues with the fingerprint sensor’s functionality. These problems can range from minor issues to severe software glitches.
Solution: Restart Your Pixel Device
One of the easiest and simplest solutions is to restart your Pixel phone. You can do that by pressing the “Power” and the “Volume Up” keys. It will lead to a pop-up power menu where you must choose “Restart” to reboot your device.
![]()
3. Outdated Firmware
Problem
An outdated operating system or firmware can lead to compatibility issues. This can lead to malfunctioning features like the Pixel 6A fingerprint sensor not working.
Solution: Check for Updates
The best way to resolve this issue is to update your Pixel device. Having an outdated version of Android OS can lead to an accumulation of bugs and glitches. Moreover, it can seriously affect the Xiaomi Redmi K70 device’s performance, causing many issues. Here is how to check and update your Pixel phone:
Instructions. On your Pixel device, access the “Settings” app. Within Settings, scroll down to tap the “System” option. On the following screen, hit the “System update” option to check if any latest update is available. Here, if you see any updates, download and install them promptly. Before initiating the update, ensure your device is connected to a stable Wi-Fi network with sufficient battery charge.
![]()
4. Dirty Phone or Sensor
Problem
Accumulated dirt, dust, or residue on the phone or fingerprint sensor can cause obstruction. This can lead to the failure to properly recognize your fingerprint.
Solution
1. Cleaning the Phone
Employ a gentle, dry microfiber cloth for wiping down the complete surface of your Pixel device. Take particular care to thoroughly clean the region surrounding the fingerprint sensor. Refrain from utilizing rough substances or strong chemicals as they could potentially cause harm to the Xiaomi Redmi K70 device.
2. Fingerprint Sensor Cleaning
Gently wipe the fingerprint sensor area using a clean, dry cloth to ensure thorough cleaning. For better results, consider using a dampened cotton swab with water or isopropyl alcohol. Before using it again, ensure the sensor is entirely dry.
3. Compressed Air or Soft Brush
Use compressed air or a soft brush if there’s visible debris or particles around the sensor. Be cautious not to apply excessive pressure that might damage the sensor.
![]()
5. Screen Protector: Dirty or Damaged
Problem
A smudged or impaired screen protector might disrupt the working of the fingerprint sensor. This can potentially cause it to fail to recognize your fingerprint.
Solution
1. Clean the Screen Protector
Start by effectively cleaning the screen protector on your Pixel device. For a thorough cleaning, consider utilizing a screen cleaning solution. Ensure that the screen protector is free from any dirt or debris.
2. Replace Damaged Protectors
Is the screen protector visibly damaged, scratched, or peeling off? If yes, consider replacing it with a new one. Damaged protectors can hinder fingerprint recognition and compromise device protection.
3. Check Compatibility
Ensure the screen protector is designed to be compatible with fingerprint sensors. Some protectors may obstruct or interfere with the sensor’s functionality.
4. Remove Air Bubbles
There can be air bubbles trapped under the screen protector. If there are, gently press them out towards the edges using a card designed for this purpose.
![]()
6. Clean Your Finger
Problem
The problem may lie with your fingers rather than the Xiaomi Redmi K70 device. Unclean or moist fingers can hinder accurate fingerprint recognition on the sensor, causing the Xiaomi Redmi K70 fingerprint sensor to not work.
Solution
1. Cleanse and Dry Your Hands
Remove any dirt, oil, or moisture that might cause issues with the fingerprint sensor. It’s crucial to wash and thoroughly dry your hands. Additionally, verify that your fingers are entirely dry before engaging the sensor. The reason is any moisture or dampness may cause inaccuracies in fingerprint identification.
2. Avoid Oily or Greasy Substances
Refrain from touching oily or greasy surfaces before using the fingerprint sensor. These substances can transfer onto your fingers, affecting sensor accuracy. If your fingers are dirty or damp, pause to clean them using a dry, clean cloth.
![]()
7. Covering Screen if Fingerprint on Screen
Problem
Fingerprint marks or smudges on the screen might disrupt sensor functionality. This leads to inaccurate recognition when you try to unlock your device.
Solution
1. Avoid Covering the Sensor Area
Be cautious while cleaning the screen to avoid covering or smudging the area around the fingerprint sensor. Precise cleaning around this area prevents interference with sensor functionality.
2. Use Proper Holding Technique
While holding the Xiaomi Redmi K70 device, avoid placing your fingers or palms over the fingerprint sensor. Opt for holding the Xiaomi Redmi K70 device to minimize accidental contact with the sensor area.
![]()
8. Fingerprint Sensor Not Visible
Problem
Misconfigured settings on your Pixel device can lead to situations where the fingerprint sensor is not visible. It can lead to scenarios where the Xiaomi Redmi K70 device fails to recognize your screen unlocking attempt.
Solution: Adjust the Setting To Consistently Display the Sensor
You must adjust the display settings to ensure the fingerprint sensor is always visible. To do that, you can begin by opening the Settings app. Navigate to the “Display” tab and select “Lock Screen.” On the following window, toggle on “Always show time and info.”
![]()
9. Low Touch Sensitivity
Problem
The fingerprint sensor may have low touch sensitivity . It can lead to difficulties in accurately recognizing fingerprints, leading to Xiaomi Redmi K70 fingerprint not working.
Solution
1. Adjust Sensitivity Settings
Accessories like a screen protector might impact the performance of your Pixel device’s touch sensitivity. When using a screen protector, your Pixel enhances touch sensitivity. To do that, navigate to the Settings app and open it. Move to the “Display” window and scroll down to the last option. Toggle on the “Screen protector mode” to increase the screen sensitivity.
![]()
2. Finger Re-Enrollment
Delete existing fingerprints and re-register them. This re-enrollment can sometimes improve sensitivity and help remove the issues. Here is how you can delete and re-enroll your fingerprint:
- Step 1. In the Settings app of your Pixel, tap “Security & Privacy.” Then, press “Device Unlock” and choose “Fingerprint Unlock.” The device will now ask you to provide your device PIN or password.
![]()
- Step 2. Tap “Fingerprint Unlock” on the following screen and delete the previously enrolled fingerprints. Then, press “Add fingerprint” and follow the on-screen prompts to complete the process.
![]()
10. Other Hardware Issues
Problem
Persistent fingerprint sensor problems might indicate underlying hardware issues . This could go beyond common troubleshooting and might require professional help.
Solution
1. Inspect for Physical Damage
Thoroughly examine your Pixel device for any physical damage. These include cracks, dents, or scratches around the fingerprint sensor area. Physical damage could affect the sensor’s functionality.
2. Safe Mode Check
Boot the Xiaomi Redmi K70 device in safe mode to determine if third-party apps are causing conflicts. To do that, press the “Power” key with any volume key to access the power menu. Afterward, long-press the “Power Off” option until the “Reboot to Safe Mode” option appears on your device’s screen. Press “OK” to reboot into Safe Mode and test the fingerprint sensor’s functionality.
![]()
3. Professional Assessment
If you suspect hardware issues, seek professional help from authorized service centers. A clear sign of hardware issues can be visible damage or the sensor failing to function even in safe mode.
11. Factory Reset as Last Resort
Problem
Did all other troubleshooting methods fail to resolve persistent fingerprint sensor issues? Then, a factory reset might be required to revert the Xiaomi Redmi K70 device to its original settings.
Solution
1. Backup Data
Before initiating a factory reset, ensure that all crucial data is safeguarded. This encompasses contacts, photos, documents, and any other significant files. Use Google’s backup services or third-party apps to securely back up your data .
2. Initiating Factory Reset
Proceed with the following steps to execute a factory reset on your Pixel device:
- Step 1. On your Pixel smartphone, navigate to Settings and access the “System” tab. Here, scroll down to the bottom and tap “Reset Options.”
![]()
- Step 2. In “Reset Options,” choose “Erase All Data (Factory Reset)” to continue. Afterward, select “Erase All Data” on the next screen and follow the instructions to complete the process.
![]()
In summary, this article detailed various methods to fix the Xiaomi Redmi K70 fingerprint not working. Diverse approaches were explored, from simple steps like sensor cleaning to advanced solutions like factory resets. However, Dr.Fone stands out among these solutions as a top-tier option. It offers a secure and efficient resolution to the persistent problem of fingerprint failure on the Xiaomi Redmi K70 .
- Title: Pattern Locks Are Unsafe Secure Your Xiaomi Redmi K70 Phone Now with These Tips
- Author: Marry
- Created at : 2024-07-18 14:19:24
- Updated at : 2024-07-19 14:19:24
- Link: https://unlock-android.techidaily.com/pattern-locks-are-unsafe-secure-your-xiaomi-redmi-k70-phone-now-with-these-tips-by-drfone-android/
- License: This work is licensed under CC BY-NC-SA 4.0.






