
Top 10 Password Cracking Tools For Xiaomi Redmi A2

Top 10 Password Cracking Tools For Xiaomi Redmi A2
What is password cracking?
Password cracking process involves recovering a password from storage locations or from data, transmitted by a computer system on network. Password cracking term refers to group of techniques used to get password from a data system.
Purpose and reason of password cracking includes gaining an unauthorized access to a computer system or it can be recovery of forgotten password. There might be another reason of using password cracking technique that is for testing password strength so hacker could not hack into system.
Password cracking is normally performed thought repetitive process in which computer applies different combinations of password till the exact match.
Brute Force Password Cracking:
Term brute force password cracking may also be referred as brute force attack. Brute force password cracking is respective process of guessing password, in this process software or tool creates a large number of password combinations. Basically it’s a trail-and-error technique used by software to obtain password information from system.
A brute force attack are normally used by hackers when there is no chance of taking advantage of encrypted system weakness or by security analysis experts to test an organization’s network security .This method of password cracking is very fast for short length passwords but for long length passwords dictionary attack technique is normally used.
Time taken by brute force password cracking software to crack password is normally depend upon speed of system and internet connection.
GPU Password Cracking:
GPU is graphics processing unit, sometimes also called visual processing unit. Before talking about GPU password cracking we must have some understanding about hashes . When user enter password the password information stored in form of computer hashes using the one-way hashing algorithm.
In this password cracking technique using GPU software take a password guess and look through hashing algorithm and compare it or match it with the existing hashes till the exact match.
GPU can perform mathematical functions in parallel as GPU have hundreds of core that gives massive advantage in cracking password. GPU is much faster than CPU so that’s the reason of using GPU instead of CPU.
CUDA Password Cracking:
CUDA Compute Unified Device Architecture is a model for programming and a platform that perform computations in parallel, created by NVIDIA for graphic processing.
CUDA Password cracking includes cracking passwords using Graphics card which have GPU chip, GPU can perform mathematical functions in parallel so the speed of cracking password is faster than CPU.GPU have many 32bit chips on it that perform this operation very quickly.
We can easily access CUDA through libraries, directives and with the help of different programming languages that includes C, C++ and FORTRAN.
Password Cracking Tools
Given below is the list of Top10 Password cracking tools.
1. Cain and Abel : Top password cracking tool for Windows
Cain & Abel is one of the top cracking tool for password cracking and password recovery for Windows OS.
Cain & Abel can use techniques of Dictionary Attack, Brute-Force and Cryptanalysis attacks to crack encrypted passwords. So it only uses the weakness of system to crack password. GUI Interface of software is very simple and easy to use. But have availability limitation, tool only available for window based systems .Cain & Abel tool have many good features some of the features of tool are discussed below:
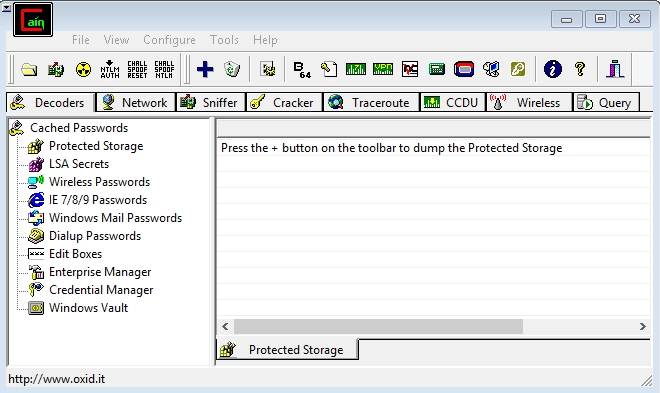
Features of Cain & Abel:
- Used for WEP (Wired Equivalent Privacy) cracking
- Have ability to record conversation over IP
- Cab be used as Network Password Sniffer
- Ability to resolve addresses IP to MAC.
- Can crack verity of hashes including LM and NT hashes, IOS and PIX hashes, RADIUS hashes, RDP passwords, and lots more than that.
Site for Download:
2. John the Ripper : Multi-platform, Powerful, Flexible password cracking tool
John the Ripper is a free multi or cross platform password cracking software. Its called multi platform as it combines different password cracking features into one package.
It’s primarily used to crack weak UNIX passwords but also available for Linux, Mac, and Windows. We can run this software against different password encryptions including many password hashes normally found in different UNIX versions. These hashes are DES, LM hash of Windows NT/2000/XP/2003, MD5, and AFS.
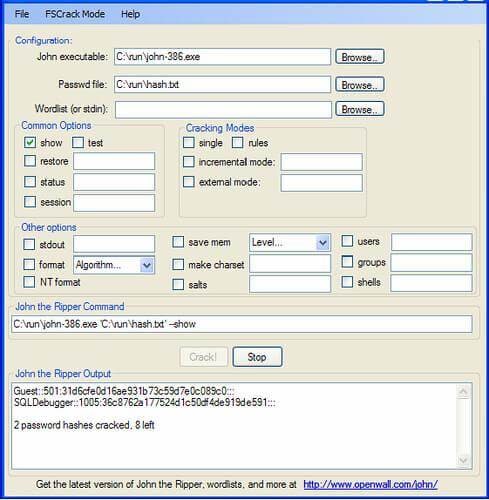
Features of John the Ripper
- Supportive with Brute force password cracking and dictionary attacks
- Multi platform
- Available free for use
- Pro version is also available with additional features
Site for Download:
3. Aircrack : Fast and effective WEP/WPA cracking tool
Aircrack is a combination different tools used for Wifi, WEP and WPA passwords cracking. With the help of these tools you can crack WEP/WPA passwords easily and effectively
Brute force, FMS attack, and dictionary attacks techniques can be used to crack WEP/WPA passwords. Basically it collects and analyzes encrypted packets then using its different tool crack password out of the packets. Although aircrack is available for Windows but there are different issues with this software if we use this in Windows environment, so it’s best when we use it in Linux environment.
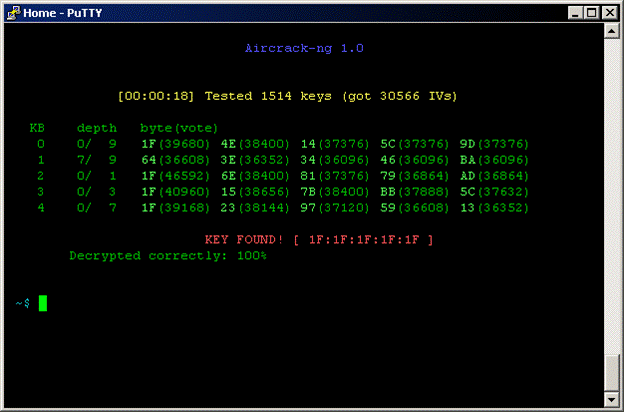
Features of Aircrack
- Supportive with both Brute force and dictionary attacks cracking techniques
- Available for Windows and Linux
- Available in live CD
Site for Download:
4. THC Hydra : Multiple services supportive, Network authentication cracker
THC Hydra is a supper fast network password cracking tool. It uses network to crack remote systems passwords.
It can be used to crack passwords of different protocols including HTTPS, HTTP, FTP, SMTP, Cisco, CVS, SQL, SMTP etc. It will give you option that you may supply a dictionary file that contains list of possible passwords. It’s best when we use it in Linux environment.

Features of THC Hydra
- Fast cracking speed
- Available for Windows, Linux ,Solaris and OS X
- New modules can be added easily to enhance features
- Supportive with Brute force and dictionary attacks
Site for Download:
https://www.thc.org/thc-hydra/
5. RainbowCrack : New Innovation in Password Hash Cracker
RainbowCrack software uses rainbow tables to crack hashes, in other words we can say it uses process of a large-scale time-memory trade for effective and fast password cracking.
Large-scale-time-memory-trade-off is a process of computing all hashes and plain text using a selected hash algorithm. After calculations, obtained results are stored in the tables called rainbow table. Process of creating rainbow tables is very time consuming but when its done software works very fast.
Password cracking using rainbow table is faster than the normal brute force attack method. It’s available for Linux and Windows operating system.
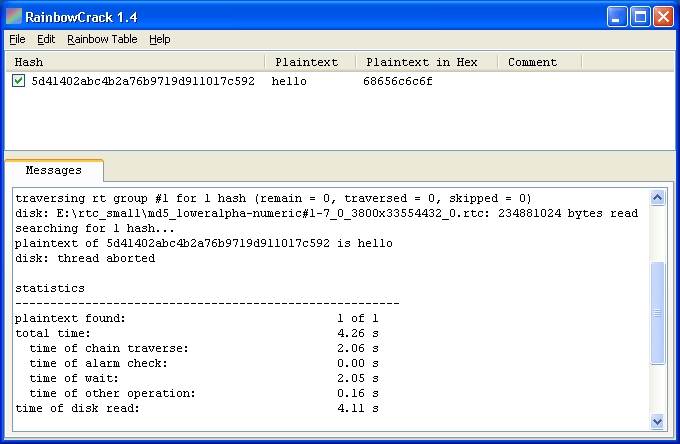
Features of Rainbow Crack
- Support verity of Rainbow tables
- Runs on Windows (XP/Vista/7/8) and Linux operating systems (x86 and x86_64)
- Simple in use
Site for Download:
http://project-rainbowcrack.com/
6. OphCrack : Tool for Windows password cracking
OphCrack used to crack Windows user passwords with the help of rainbow tables that are available in a bootable CD.
Ophcrack is completely free to download, Windows based password cracker that uses rainbow tables to crack Windows user passwords. It normally cracks LM and NTLM hashes. Software has simple GUI and can runs on different platforms.
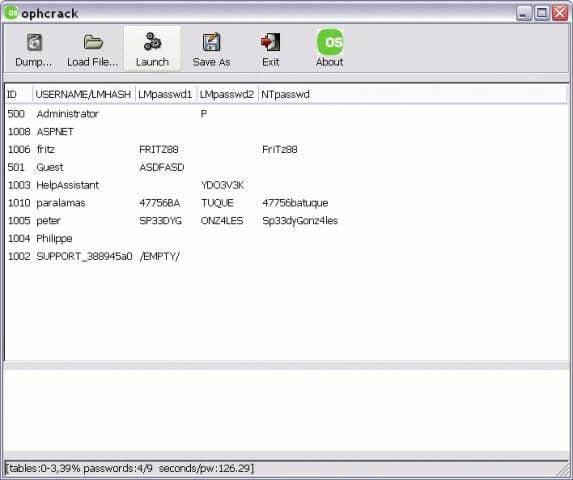
Features of OphCrack
- Available for Windows but also available for Linux, Mac, Unix, and OS X
- Uses for LM hashes of Windows and NTLM hashes of Windows vista.
- Rainbow tables available free and easily for Windows
- To simplify the process of cracking Live CD is available
Site for Download:
http://ophcrack.sourceforge.net/
7. Brutus : A brute force attack cracker for remote systems
Brutus is the fastest, most flexible, and most popular software used to crack remote system passwords. It guess password through applying different permutations or by using a dictionary.
It can be used for different network protocols including HTTP, FTP, IMAP, NNTP and other types such as SMB, Telnet etc. It also gives you facility of creating your own authentication type. It also includes extra options of load and resume, so process can be paused when required and you can resume process when you want.
It is only available for windows operation systems. Tool has a limitation that it has not been updated since 2000.

Features of Brutus
- Available for Windows
- Can be used with different network protocols
- Tool have many good extra features
- Support SOCK proxy for all types of authentications
- Capability of error handling and recovery
- Authentication engine is multi stage
Site for Download:
8. L0phtCrack : Smart tool for Windows password recovery
Just like OphCrack tool L0phtCrack is also a Windows passwords recovery tool uses hashes to crack passwords, with extra features of Brute force and dictionary attacks .
It normally gains access to these hashes from directories, network servers, or domain controllers. It is capable of doing hash extraction from 32 & 64 bit Windows systems, multiprocessor algorithms, scheduling, and can also perform decoding and monitoring networks. Yet it is still the easiest to use password auditing and recovery software available.
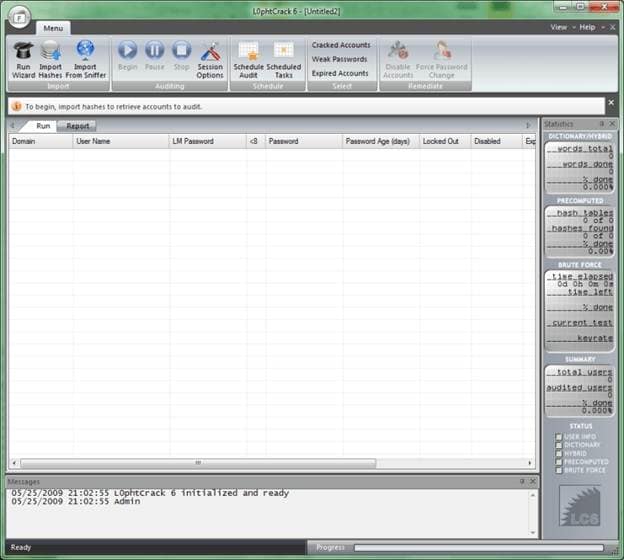
Features of L0phtCrack
- Available for Windows XP, NT, 2000, Server 2003,and Server 2008
- Can work in both 32- and 64-bit environments
- Extra feature of schedule routine auditing on daily, weekly, monthly bases
- After run it provide complete Audit Summary in report page
Site for Download:
9. Pwdump : Password recovery tool for Windows
Pwdump is actually different Windows programs that are used to provide LM and NTML hashes of system user accounts.
Pwdump password cracker is capable of extracting LM, NTLM and LanMan hashes from the target in Windows, in case if Syskey is disabled, software has the ability to extract in this condition.
Software is update with extra feature of password histories display if history is available. Extracted data will be available in form that is compatible with L0phtcrack.
Recently software is updated to new version called Fgdump as Pwdump not work fine when any antivirus program is running.
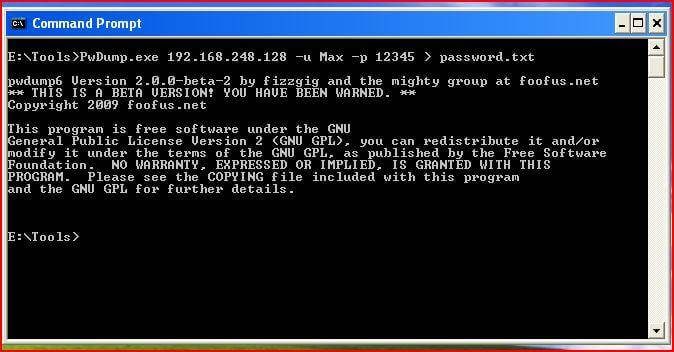
Features of Pwdump
- Available for Windows XP, 2000
- Powerful extra feature are available in new version of Pwdump
- Ability to run multithreaded
- It can perform cachedump (Crashed credentials dump) and pstgdump (Protected storage dump)
Site for Download:
10. Medusa : Speedy network password cracking tool
Medusa is remote systems password cracking tool just like THC Hydra but its stability, and fast login ability prefer him over THC Hydra.
It is speedy brute force, parallel and modular tool. Software can perform Brute force attack against multiple users, hosts, and passwords. It supports many protocols including AFP, HTTP, CVS, IMAP, FTP, SSH, SQL, POP3, Telnet and VNC etc.
Medusa is pthread-based tool, this feature prevent unnecessarily duplicate of information. All modules available as an independent .mod file, so no modification is required to extend the list that supports services for brute forcing attack.
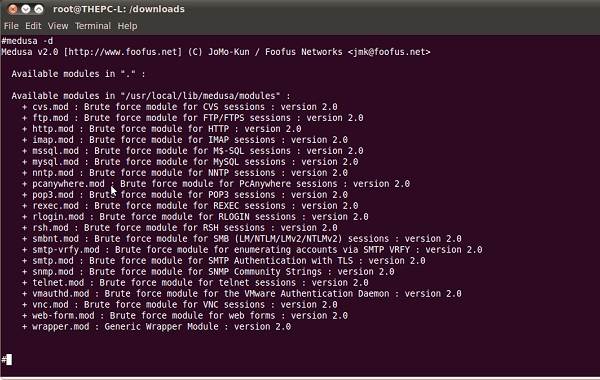
Features of Medusa
- Available for Windows, SunOS, BSD, and Mac OS X
- Capable of performing Thread based parallel testing
- Good feature of Flexible user input
- Due to parallel processing speed of cracking is very fast
Site for Download:
How to Remove a Previously Synced Google Account from Your Xiaomi Redmi A2
The setting up process of a new Android phone requires you to add a Google account that saves all activities and data of the phone like search history, details of online shipping, play store purchases, and more. Once the account is set, it cannot be changed till you delete everything from your phone. Moreover, with the introduction of FRP lock, even a factory reset will not remove the synced Google account.
So, now what if you want to sell your phone or have purchased a second-hand device that is still associated with the previous owner’s Google account? No, worries as there are workarounds available that will help you remove your previously synced google account from your Android device.
Keep reading to know more in detail about how to bypass previously synced google accounts.
Heres a full guide on how to remove google account from android, click to know more!
Part 1: Remove Previously Synced Google Account from Android Phone Without Phone Reset
In this part, we will discuss the methods that can be used for removing the previously synced account from your Android phone without a phone reset.
Method 1: Removing Google Account using the Android Settings Menu
If you just plan to reset your phone, maybe because of the lag caused by the phone cache, and you know the inconvenience of Google FRP as a protection mechanism, then you can remove Google FRP through the Settings menu.
The steps for this method are listed below.
- Step 1: On your Android phone go to the Settings option and choose Accounts & Backup.
- Step 2: Select the Manage Accounts option now and the list of the associated Google Devices will appear.
- Step 3: Choose and click on the Google Account that you want to remove and a pop-up message will appear to inform you that all the account data will be deleted with this action.
To confirm the removal of the account, click on the Remove account button.
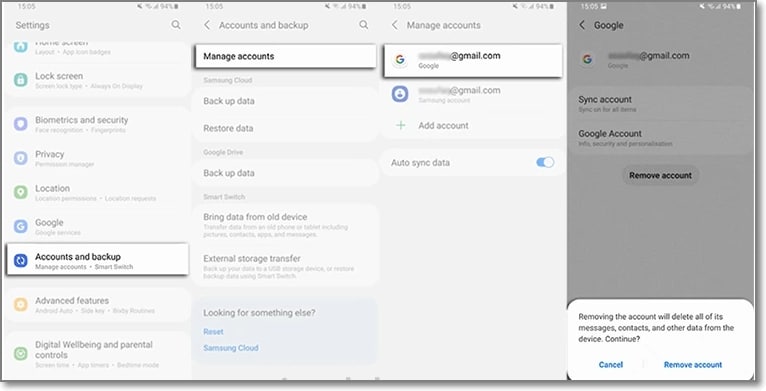
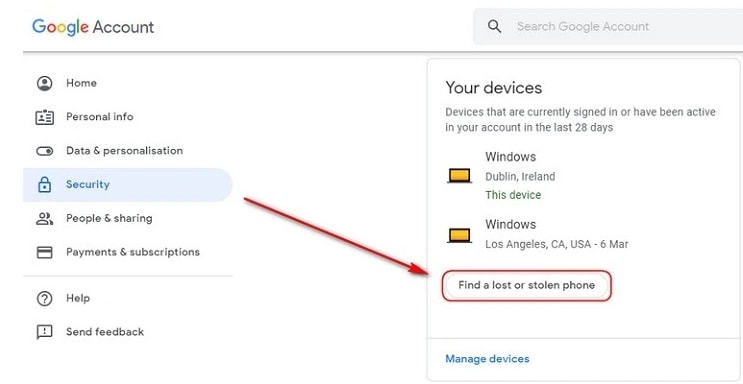
Method 2: Remove the Google account from the Android phone using the computer
There is another method using which you can remotely remove the Google account associated with your phone. The steps for the method are listed below.
- Step 1: Using another device or a PC, sign in to your Google account that was previously synced on this device and choose the Security option.
- Step 2: Next scroll down and then tap on the Your devices option and choose to Manage devices.
- Step 3: You will now see the list of devices linked to your Google account. Next, tap on Find a lost or stolen phone and then select the Remove option present next to Account access.
- Step 4: You will be again asked if you want to delete the account. Select the Remove option.
- Step 5: The account will be removed successfully and the confirmation message will appear.
Note: This method will actually sign out you from the Google account and will not delete it permanently. To again get access to the account, a notification will appear on your phone to enter the password.
Part 2: How to Disable Factory Reset Protection to Bypass Google Account Verification After Factory Reset
The Factory Reset Protection (FRP) is a security feature for the Android device that allows factory reset only after the associated Google ID and password are entered correctly. With multiple accounts and passwords to remember there is quite a possibility that you may forget your Android phone Google account details and here the need to bypass Google account verification arises.
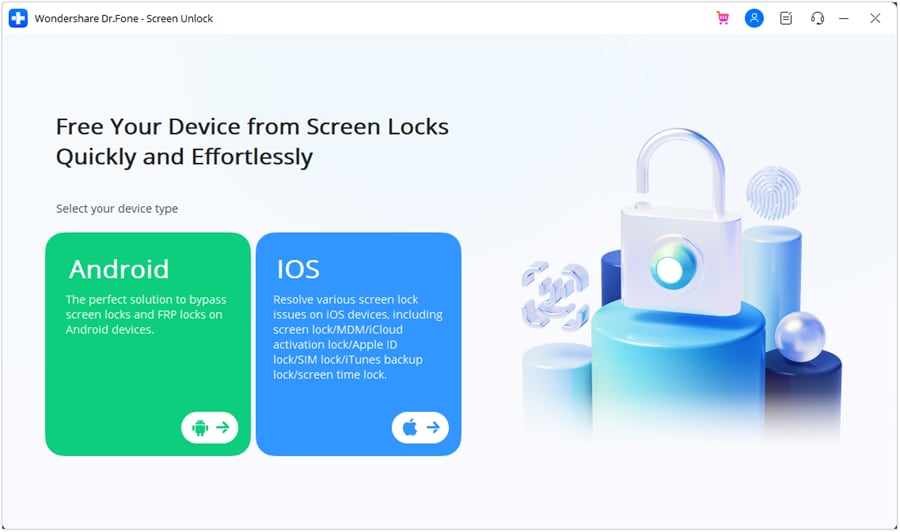
Though there are multiple tools available we recommend Dr. Fone - Screen Unlock (Android) as the best and the most reliable option. Using this excellent Windows and Mac-based software, FRP lock on all popular Android devices including Samsung, LG, HTC, and others. The tool is simple to use and requires no technology. There is also an option where you can unlock your device if you do not know the OS version.

Dr.Fone - Screen Unlock (Android)
Get into Locked Phones within Minutes
- 4 screen lock types are available: pattern, PIN, password & fingerprints.
- Easily remove the lock screen; No need to root your device.
- Everybody can handle it without any technical background.
- Provide specific removal solutions to promise good success rate
4,008,669 people have downloaded it
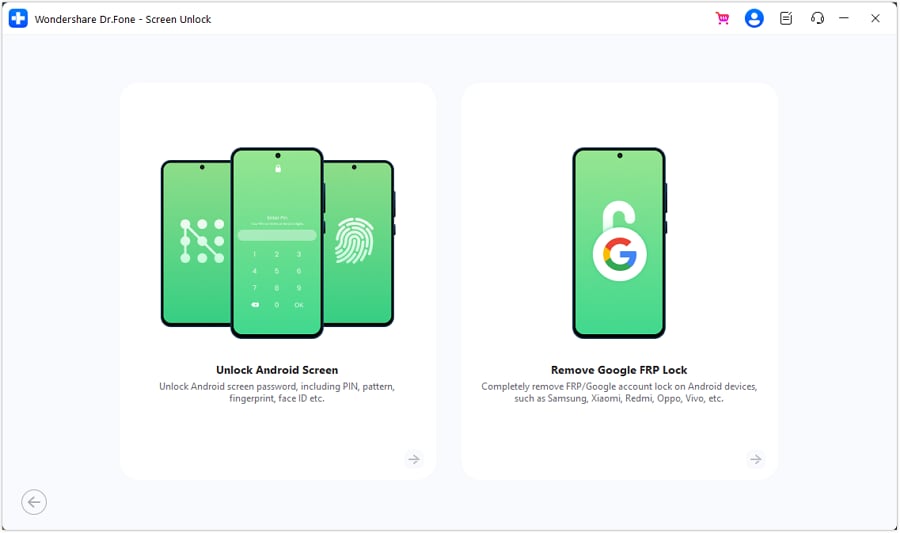
Steps to remove FRP lock using Dr. Fone-Screen Unlock (Android)
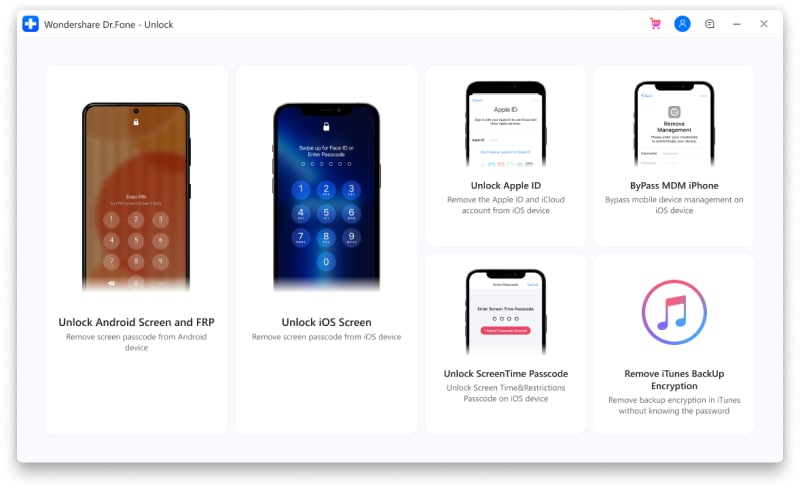
Step 1: Download, install and run the software on your system, and from the main interface choose the Screen Unlock option. Make sure that your phone is connected to WiFi.
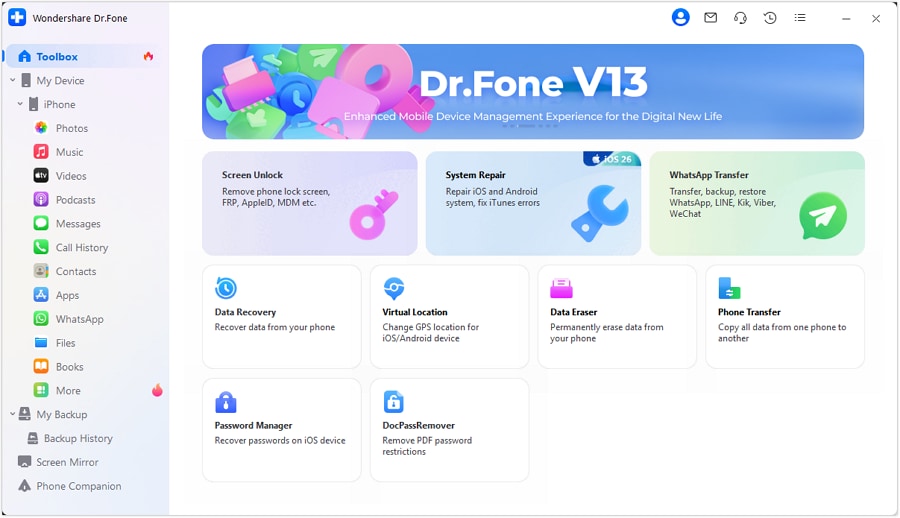
Step 2: Next, choose Unlock Android Screen/FRP and then select the Remove Google FRP Lock option.
Step 3: Next, choose the OS version of your device from the given options, and then using a USB cable, connect your phone to your system.
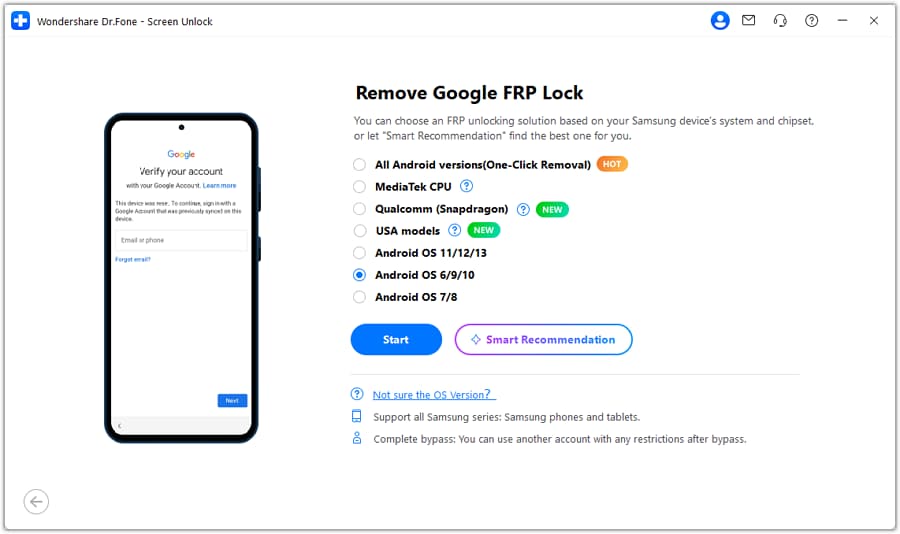
Step 4: After the Xiaomi Redmi A2 device is connected, the Xiaomi Redmi A2 device information will appear on the software for you to confirm and the notification for the same will be sent to your Android phone.
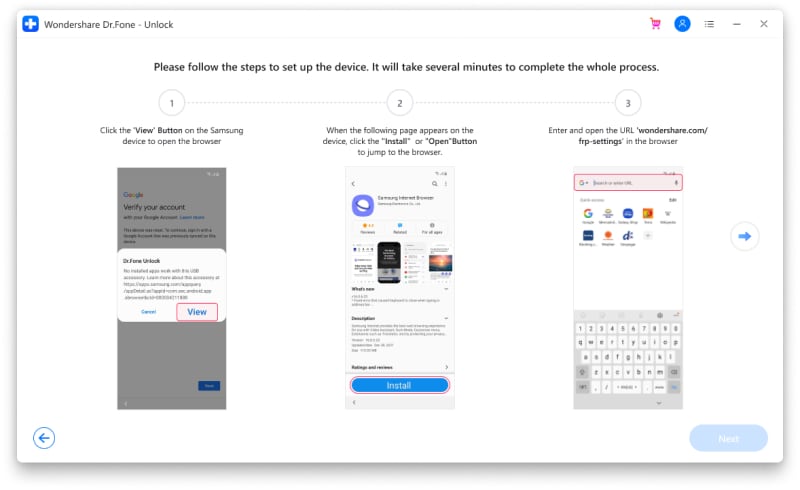
Step 5: Now follow the notifications for removing the FRP lock and in the browser enter drfonetoolkit.com.
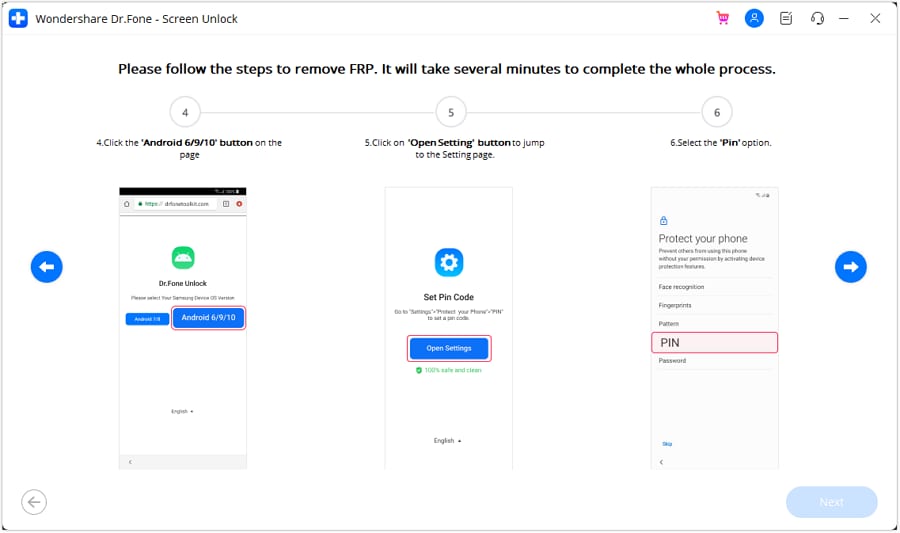
Step 6: Next, click on the Android 6/9/10 button, choose Open Settings and select the PIN option to set a PIN to be used in the further steps.
Step 7: Keep following the steps as they appear till you reach the Google Account Sign-In page. Here click on the Skip option that will successfully remove and bypass the Google Account.
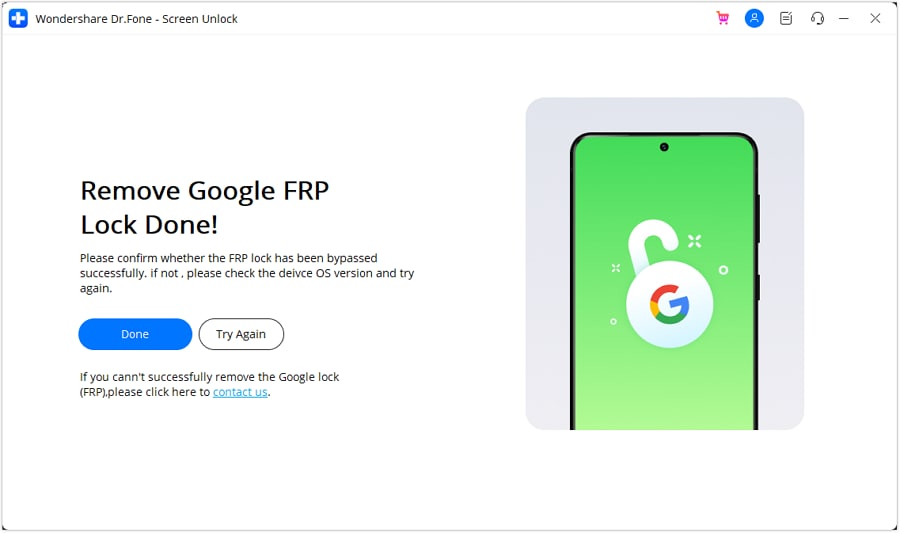
The above given are the brief steps for the FRP bypass process. To learn about the entire process in detail, check Dr.Fone-Screen Unlock (Android) guide .
Part 3: Hire a Remote FRP Removal Service to Bypass ZTE/Motorola After Factory Reset
To bypass the FRP lock on your ZTE, Motorola, and Samsung device, there is also an online service called UnlockJunky.com that claims to remove the FRP lock and previously linked account on your Android device within 5-15 minutes. This is a paid service that also claims that if they are unable to remove the lock, they will refund the amount to their customers.
So, if you cannot sign in with a Google account that was previously synced, you can give this, method a try.
Step 1: Open the official service page Unlockjunky on your browser.
Step 2: Next, choose the Xiaomi Redmi A2 device’s brand, model, and unlock type from their respective drop-down menus. Click on Unlock Now button after entering the details.
Step 3: Now you need to initiate the order by providing the details asked and completing the payment.
Step 4: Next, the software needs to be downloaded and installed on your system, and using a USB cable, connect your phone to your computer.
Step 5: Connect with one of the support provider members through the live chat and they will help you remove the FRP lock on your Android phone.
With the steps above, you can remove the account previously synced on this device.
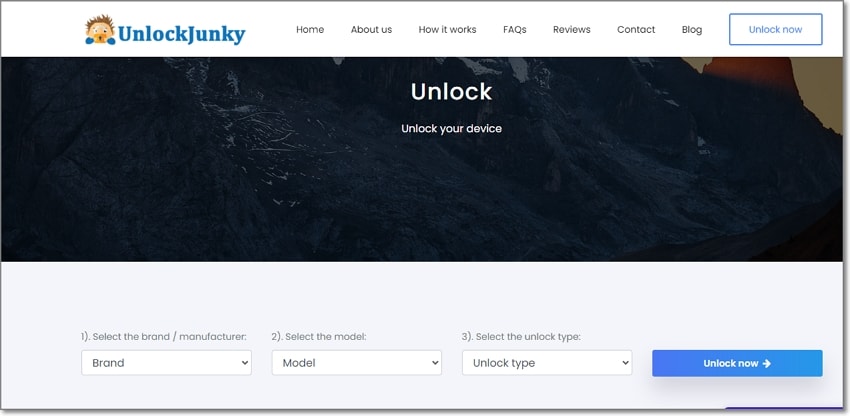
Limitations of using the Unlockjunky method:
- This is a paid service.
- Works only with Motorola, ZTE, and Samsung devices.
- There is no surety that the service will work for removing the FRP lock on your devices.
- If you have to remove the FRP lock from multiple devices, a separate payment for each device has to be done.
Conclusion
Above we have listed several ways to remove a previously synced Google account on your Android device. The best of all the listed solutions is Dr. Fone - Screen Unlock (Android) as it supports bypassing FRP lock on multiple Android devices in a hassle-free manner. Once the license is purchased, you can unlock as many numbers of devices as you want without any worries.
Top Apps and Online Tools To Track Xiaomi Redmi A2 Phone [With/Without IMEI Number]
Losing your smartphone can be distressing, given its importance in daily life. Ensuring the ability to trace the whereabouts of a misplaced device holds great importance. It is due to potential theft, loss, or accidental misplacement.
Fortunately, many ways exist to retrieve a lost mobile phone by utilizing its IMEI number. This article will take you through the anti-theft app & IMEI tracker of all phone location methods. Additionally, we will discuss a unique tool designed to unlock locked devices.
Part 1: An Introduction to IMEI Numbers and Its Utility
Every mobile device has a special identifier that is helpful in the anti-theft app & IMEI tracker activities. It is known as the International Mobile Equipment Identity or IMEI number. While often overlooked, it holds the key to many essential services and functions.
This makes it an indispensable component of modern mobile technology. The IMEI number serves as a digital fingerprint for mobile phones. Its primary purposes are summarized below:
- Device Identification: Each mobile device possesses a distinct IMEI number. This sets it apart from every other phone in existence. This identification is essential for cellular networks and service providers. It helps in recognizing, managing, and connecting devices accurately.
- Traceability and Tracking: In cases of theft, loss, or unauthorized use, the IMEI number becomes a crucial tool for tracking. It provides law enforcement agencies with the means to pinpoint the Xiaomi Redmi A2 device’s location.
- Warranty and Support: Manufacturers use IMEI numbers to manage warranties and provide technical support. These numbers help confirm the Xiaomi Redmi A2 device’s authenticity, purchase date, and warranty coverage. This streamlines the process of repairs and replacements.
- Security Measures: IMEI numbers play a role in security measures such as device blacklisting. If a device is reported stolen, its IMEI number can be added to a global database. This prevents it from being used on any network and renders it useless to thieves.
Part 2: A Dedicated Android Solution To Track Phone Location Using IMEI Number
IMEI numbers are important for more than just working as identifiers. One practical application lies in tracking a lost or stolen phone. It is a scenario that can cause significant distress. To address this concern, a great solution is the “AntiTheft App - IMEI Tracker, All Mobile Location.”
It is a dedicated Android app designed to harness the power of IMEI numbers for phone tracking. This anti-theft app & IMEI tracker provides a comprehensive method to locate a misplaced or stolen device. Its core work revolves around using the IMEI number to find the Xiaomi Redmi A2 device’s location. With it, you can send commands via SMS (text messages) from an alternate device.
![]()
These functionalities encompass using secure commands with a designated secret code. Using these commands, you can have the smartphone ring audibly at its maximum volume. It can also get the GPS coordinates of the Xiaomi Redmi A2 device. You can also display a personalized message across the screen. Lastly, it can even capture photographs through the front-facing camera.
Part 3: Online Solutions: Finding The Best Anti-Theft Online Tool Using IMEI Tracking
The internet makes it easy to deal with lost or stolen devices. Online solutions offer another way to find your smartphone using IMEI tracking. In contrast to conventional approaches, these digital tools enhance the efficiency of the process.
They provide a ray of optimism, even for individuals with limited tech proficiency. Below are two prominent anti-theft apps & IMEI trackers online that use IMEI tracking to aid in phone location:
Method 1. IMEI-Tracker
The purpose of this web-based platform is to streamline the procedure for locating a misplaced or stolen mobile phone. With just the IMEI number of your lost device, you can ascertain its GPS coordinates. Employing sophisticated algorithms, the platform triangulates the rough whereabouts of the Xiaomi Redmi A2 device. The following steps outline how to use IMEI-Tracker to find the location of your lost device:
- Step 1: Begin by accessing a web browser on a device and navigate to the IMEI-Tracker.com website. Here, click “Track IMEI” to access the IMEI tracking feature.
- Step 2: On the next page, enter your lost device’s IMEI number and select the country. Afterward, click “Track IMEI” to kickstart the tracking process.
![]()
Another player in the online IMEI tracking space is TrackIMEI.net. It offers a user-friendly approach to locating missing devices. By inputting the IMEI number into the platform, you can pinpoint the location of your device. This service also facilitates the reporting of lost or stolen devices. Use the following steps to locate your device via TrackIMEI.net.
- Step: On a web browser, access TrackIMEI.net and type your IMEI number in the text field. Then click “Search” to initiate the search for your lost device.
![]()
Part 4: Anti-Theft Apps That Locate Devices Without IMEI
Anti-theft apps offer a mean to locate a device even without relying on the IMEI number. These apps provide an alternative route to safeguard your valuable possessions. Moreover, these apps offer an extra layer of security and assurance. Below are two noteworthy anti-theft apps that enable users to track their devices:
Method 1. Find My Device (IMEI Tracker)
Available on the Play Store, the Find My Device (IMEI Tracker) is a popular choice among users. It allows you to experience the utmost simplicity in tracking your Android device. With this cutting-edge GPS tracker, you can effortlessly track your Android phone.
To activate the tracking function, the app must be installed on the targeted phone. After installing the anti-theft app & IMEI tracker, you can use the website to track the Xiaomi Redmi A2 device’s location.
![]()
Method 2. Anti-Theft Mobile Tracker
The Anti-Theft Mobile Tracker app provides an innovative approach to tracking devices. It allows the transmission of the precise location of the lost device to a recipient device. This functionality operates without requiring an active Internet connection.
The anti-theft app & IMEI tracker for all mobile locations enables remote actions, including locking the Xiaomi Redmi A2 device and erasing personal data. Through this app, users can lock their phones and safeguard their data from a distance.
![]()
Bonus Part: Got Your Xiaomi Redmi A2 Locked? Unlock It Easily With the Best Third-Party Utility
Losing access to our own devices due to a forgotten password or lock pattern can be exasperating. In such cases, a reliable third-party utility, Wondershare Dr.Fone, comes to the rescue. It offers a seamless method to regain access and control over your precious devices. It is designed to provide a straightforward way to unlock locked Android devices.
The utility offers different unlock modes to cater to various scenarios. These include PIN, pattern, password, and even fingerprint or facial recognition. Wondershare Dr.Fone boasts a high success rate in unlocking devices, making it a reliable option.

Dr.Fone - Screen Unlock (Android)
The Best UnlockJunky Alternative to Bypass FRP and Solve Your Screen Locks
- Completely unlinked from the previous Google account, it won’t be traced or blocked by it anymore.
- Remove all Android screen locks (PIN/pattern/fingerprints/face ID) in minutes.
- Almost all Samsung phones and tablets are supported (Currently for Android 6-13).
- Provide specific removal solutions to promise good success rate.
4,008,671 people have downloaded it
Prominent Features of Wondershare Dr.Fone
- When unlocking a locked Android Phone, like a Samsung or LG device, with Dr.Fone, you can do it without data loss.
- It allows you to bypass Google FRPlock on all major Android brands like Samsung, Mi, OPPO, etc.
- With Wondershare Dr.Fone, you can unlock screen locks such as PIN, password, pattern, and fingerprint.
Unlocking your locked Android device using Wondershare Dr.Fone is a straightforward process. Here’s a simplified step-by-step guide to help you through the process of unlocking your Android screen lock:
- Step 1: Navigate to Screen Unlock in Wondershare Dr.Fone
You start with launching Wondershare Dr.Fone on your computer. Navigate to “Toolbox” and access “Screen Unlock.” On the following screen, choose “Android” as your device type.
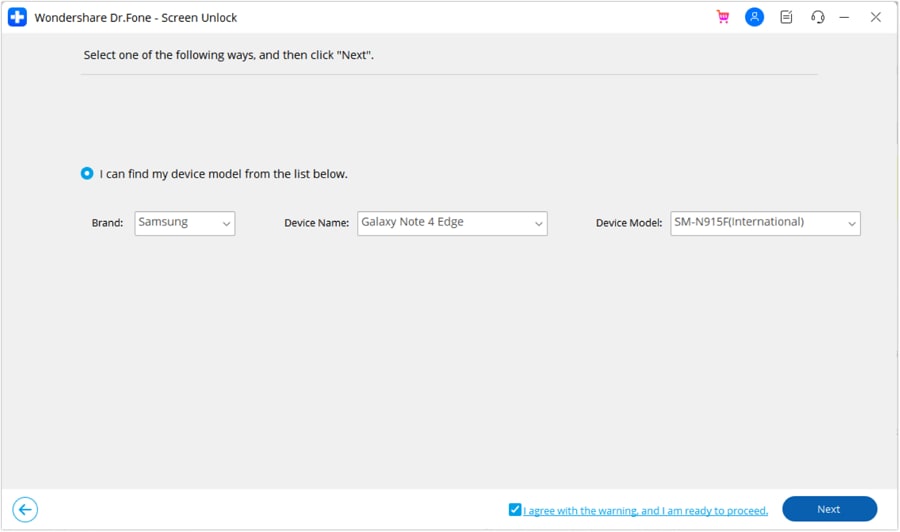
- Step 2: Choose Your Xiaomi Redmi A2 Device Brand
After choosing the Xiaomi Redmi A2 device type, select “Unlock Android Screen”. Now choose the brand of your Android, for example, Samsung, and on the next screen, click “Remove without Data Loss”. Following this, you need to input the “Brand”, “Device Name”, and “Device Model” of your smartphone.
- Step 3: Agree to the Android Screen Unlock Terms
Enable the checkbox that indicates your agreement with the warning and your readiness to proceed. Then, proceed by clicking the “Next” button to unlock the screen. A confirmation step will appear, asking you to enter the code “000000”. Once you’ve entered the code, click on “Confirm” to carry out the necessary operation.
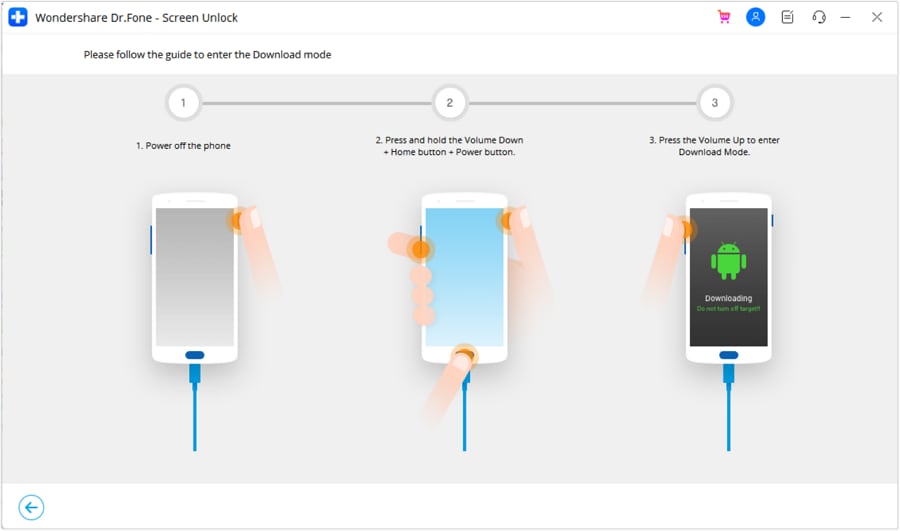
- Step 4: Unlock Your Locked Android Device
The final step is to put your Android device into Download Mode. To make it easier for you, the instructions are given on the screen. As soon as the Download Mode is activated, the Android screen unlock process will start. Click “Done” once the process has been completed.
Conclusion
In short, it can be scary to lose your smartphone due to theft, misplacement, or unauthorized access. During our exploration, we discovered many ways to locate your device if you lose it. The “Anti-theft App & IMEI Tracker All Phone Location“ stands out as a beacon of hope. It provides a dedicated Android solution to locate devices even in adverse situations.
As a bonus, Wondershare Dr.Fone emerged as a powerful ally for those locked out of their devices. This Android screen unlock toolkit offers a user-friendly interface and a high success rate. To conclude, as technology continues to evolve, your ability to safeguard your devices and data becomes robust.
- Title: Top 10 Password Cracking Tools For Xiaomi Redmi A2
- Author: Marry
- Created at : 2024-07-18 13:35:07
- Updated at : 2024-07-19 13:35:07
- Link: https://unlock-android.techidaily.com/top-10-password-cracking-tools-for-xiaomi-redmi-a2-by-drfone-android/
- License: This work is licensed under CC BY-NC-SA 4.0.



